When Trust Became a Thing You Had to Earn
At one time, trust was a default. You turned on the news, read the paper, and just believed what it said — not because you were dumb, but because it seemed like the machine actually worked. It had standards. It had gatekeepers. No one questioned it. And that, in retrospect, was the entire problem.
Then 2016 happened. "Fake news" entered the cultural vocabulary like a virus. Along with it came coordinated disinformation, foreign interference, and bots that helped amplify lies at scale. The baseline credibility institutions had earned over years was hemorrhaged in months. Cracks widened fast:
- Speculation about election meddling eroded confidence in every outlet simultaneously
- The realization that the system could lie at scale, systematically
- Audiences suddenly aware they'd been trusting blindly for years
It wasn't paranoia. It was an answer to a truly broken information environment — which somehow ends up being worse. Because once you see the machinery is compromised, you can never unsee it.
In a flash, muscle memory flipped: from trust by default, verify if suspicious — to verify before accepting, trust rarely, keep receipts. Every channel became suspect until proven otherwise. Every outlet. Every platform. The shift wasn't incremental. It was seismic.
AI Made It Worse
When did you stop trusting what you saw?
Because AI didn't just crack the foundation of our trust — it obliterated it. Text that sounded like it was written by a human. Images that had never existed. Video of people saying things they'd never said, moving in ways they'd never moved. Deepfakes. Synthetic media so clean you couldn't tell them apart. Seeing stopped meaning believing.
Authentic content suddenly got a burden it never had before: the demand for provenance. The real stuff also needs proof. Needs papers. Needs you to verify it before you accept it.
The questions shifted from "is this source reliable?" to "is this real at all?" Distrust stopped being the rational response to a broken system and became the ambient condition. The baseline. The water you swim in.
The sequence locked in:
- Audiences stopped trusting outputs — both human and machine-generated
- Institutions realized they needed to prove things they once assumed — systems that could verify without asking anyone to just believe
- The problem migrated downstream — from "is the media lying?" to "can I trust this transaction?" to "can these machines talk to each other without someone lying?"
The Same Problem Moved Into Digital Transactions
Distrusting the media was just the start. Things got worse when it moved into money.
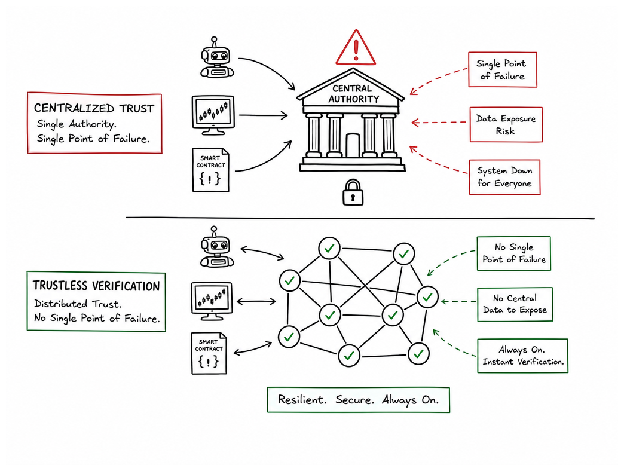
Digital transactions are just verifiable claims: that you're eligible for a trade, own an asset, have a certain account balance, or are who you say you are. Legacy systems took the logical approach — centralize trust with a trusted party. Your bank checks your balance. A government-issued ID proves your identity. Certificate authorities verify your encryption keys. Simple. Until it isn't.
Centralized trust means there is only one point of failure — and every hacked database proves it. Each breach exposes millions. When any authority becomes corrupt, it poisons the entire chain. But here's the even darker problem that nobody talks about until it's too late:
- Machine-to-machine systems can't wait. IoT devices, smart contracts, automated trading algorithms operate at machine speed. They don't stop and call central authority to ask "Hey, is this legit?" By then, the opportunity's gone.
- Frictionless verification feeds the beast. Verify claims instantly without friction and they'll not only multiply — they'll explode. Traders build algorithms that exploit the gaps between verification cycles. Market dynamics move toward the speed of electricity. The slowest verifiers get buried.
- Data exposure scales with every transaction. The more you centralize, the more you accumulate. The more claims you verify, the more data sits in one location. The more surface area for an attack — and the more incentive to take it all down.
The demand emerges hard and clear: verify claims instantly without revealing the underlying data. Prove you own the asset without showing the ledger. Prove you're eligible without exposing your identity.
This is where it collides with cryptography — and the whole game changes.
Zero-Knowledge Proofs: Prove It Without Showing It
Here's the conundrum: the system needs to verify something, which means exposure. You need proof that something is true, but you don't want to share the proof. Just because you moved it online doesn't mean the problem goes away.
Here's where zero-knowledge proofs come in.
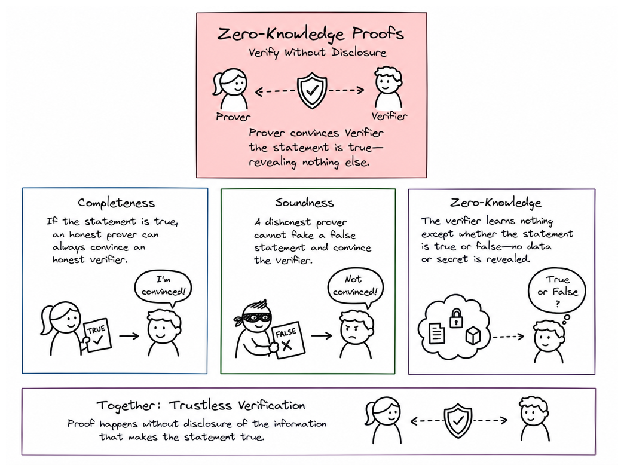
A zero-knowledge proof is a cryptographic protocol where a prover convinces a verifier that a statement is true without revealing any information beyond the statement's validity itself. It's weird enough to break your brain if you stare at it — and simple enough to tattoo on your wrist.
Three properties have to hold at the same time. Not maybe. Not approximately. All three, every time:
If the statement is true, an honest prover can always convince an honest verifier. No wiggle room, no ambiguity. You know something, you prove it — that's it. This one sounds obvious until you realize how many systems fail at it.
If the statement is false, no matter how hard a cheating prover tries, an honest verifier won't be convinced otherwise — with any significant likelihood. The math is that harsh. A liar will be caught, over and over, no matter how cunning they get.
The verifier learns one thing and one thing only — whether something is true or false. Not the secret. Not the mechanism. Not even a whisper of the underlying data. They walk away with exactly what the system needed to tell them, and that's all.
These aren't absolute mathematical certainties — they're probabilistic. But probability can be stacked so high through multiple rounds that in practice, "arbitrarily close to certain" starts looking indistinguishable from certain.
Imagine you and a verifier share a secret password. The verifier starts unsure if you really know it. You don't whisper it to them. Instead, they challenge you. You respond correctly. They ask again. Again, you answer correctly. After enough challenges, the verifier is convinced — not because you revealed anything, but because the probability that you're faking it becomes nearly zero.
No secret is exchanged. No data is leaked. Just proof.
What ZKPs Actually Unlock in the Real World
The theory is clear: a prover convinces a verifier and no actual information leaks. But here's the question that actually matters — what does this do?
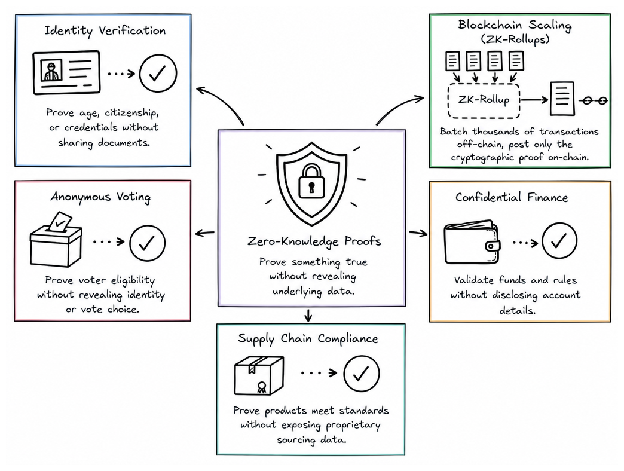
1. Identity verification without handing over your entire life
Want to prove you're over 21 without showing your birthdate? Or prove citizenship without uploading your passport to a server that's going to be hacked next Tuesday? The verifier knows only that you meet their requirements. Nothing else. Your documents stay on your side.
2. Blockchain scaling that actually works
Take thousands of unrelated transactions, batch them off-chain, and throw only the proof back on-chain. Speed explodes. Fees crater. Security stays intact — because you're trusting math, not a centralized company compressing all the traffic.
3. Voting that's anonymous and verifiable
Prove you're eligible to vote without divulging your vote or your identity. The paradox doesn't go away — you just stop needing it to.
4. Financial transactions wrapped in opacity
Confirm funds and compliance while keeping account details confidential. Every balance verifiable. Every transaction provable. Nothing visible. This is the scaffolding underneath markets that move on asymmetric information — where alpha generation depends on exactly this kind of controlled darkness.
5. Supply chain compliance without revealing your sourcing
Give proof your product meets requirements without revealing your supply chain to competitors. Transparency and secrecy coexist — simultaneously.
All of these use cases follow the same skeleton: they remove the need for a trusted middleman. The system works because it has to, not because anyone's honest. Trustless architecture that replaces the requirement for trust entirely.
The Late-Market Analogy: Why the Skeptics Arrive Last
The same thing happened every time a verification layer got built. For SSL certificates — paranoia and unnecessary overhead. For two-factor authentication — friction nobody needed. For end-to-end encryption — "security theater," they said.
Then a breach where millions of people are exposed goes viral, and the overcautious turn into prophets.
| Technology | Early Reception | Adoption Trigger |
|---|---|---|
| SSL / TLS | Oversized paranoia | Mass phishing, visible breaches |
| 2FA | Friction nobody needed | Mainstream account takeovers |
| End-to-end encryption | Security theater | Media panic + regulatory pressure |
| Zero-knowledge proofs | Technically bulletproof, not yet everywhere | The next breach. The next AI distortion event. |
ZKPs are sitting at exactly that inflection point. Asymmetric opportunity windows don't last forever. Early movers see the architecture. The crowd sees risk. By the time the crowd catches up, the edge is already gone.
Move now, when the tech is proven but nobody cares yet. Move before the regulators write the memo. Move before it's on a slide deck at McKinsey. Once everyone agrees, the asymmetric payoff evaporates.
Trustless Doesn't Mean Trustworthy — It Means Trust Is Unnecessary
Trustless is a tricky word. It sounds broken. Unreliable. But it doesn't mean the system is sketchy — it means it's mechanical rather than relational. No handshake. No vibes check. The system doesn't need to trust you. It checks the proof. You show up with cryptographic evidence, the architecture validates it, and the transaction happens. No relationship required. No middleman deciding if you deserve the nod.
This is — maybe — the architectural answer to a decade of media manipulation and AI distortion. The move isn't to fix human behavior. It's to build systems that don't require humans to behave well in the first place.
The System Isn't Honest — So Build One That Doesn't Have to Be
The system hasn't really been honest. Media, institutions, platforms — they all have their distortion points. Money funds sensationalism. Algorithms promote engagement over accuracy. People in power protect themselves. You knew this.
What if the architecture itself didn't need it?
ZKPs don't make anyone do the right thing. They're colder and more useful: they remove the requirement of humans to do the right thing. Verification happens mechanically. The proof doesn't care about your algorithm's dopamine loop or your incentive structure.
This is one problem, finally getting an architectural answer. Just like when institutional integrity broke and we needed a new layer — not just better institutions. A system where trust is no longer currency. Where verification doesn't require disclosure. Where the infrastructure of truth is built on math, not faith.
This will be the infrastructure of the next decade. Whether anyone's ready for it or not.
When Dharma Decays, Capital Compounds.